[Photo by Glen Carrie on Unsplash]
Good morning,
All of us at Founding Fuel are watching with much interest how people are migrating from messaging app WhatsApp to Signal and Telegram, citing privacy concerns. And many of them are coming back to WhatsApp because those places aren’t as action packed yet (there was privacy there, but no people, as a meme observed).
But this is a way of looking at the world in a ‘take-it-or-leave-it’ way. That isn’t how the world works or people think. There are trade-offs to be made constantly. All of us must constantly adjust to what we can gain and what must be given up. This applies to personal technology as well. But just how much must we give up so we retain our privacy?
The good news is, we need not give up as much privacy for convenience as most of us imagine, to make the most out of what technology has to offer. And if you may have some pointers, do share it with us as well.
In this issue
- FF Recommends: How to secure your privacy
- How English used to be
Have a good weekend.
FF Recommends: How to secure your privacy
As recently as October 2020, we had made a series of recommendations on how to secure your privacy. But now that WhatsApp and Facebook are under intense scrutiny for compromising user data, we think it pertinent the theme be revisited. Privacy is like a cat-and-mouse game. You must revisit all of what you do, often.
Secure your identity: If someone were to tell you there is much data about you in the public domain, and if you are not a public personality, this may come across as a ridiculous assertion. So, try this. In Google, type your name within quotes followed by the name of a file extension. For example, “Chandan Kumar” filetype:pdf. Or “Chandan Kumar” filetype:xls. Go ahead. Try it.
Chances are high some documents will tumble out of some database stored someplace that contains some details about you. This is because many Indian organizations and government departments still haven’t got their act together on how to keep information secure. For a nefarious actor looking to dredge up information about you, this is a great place to begin. Who knows what may emerge? Worst case scenarios include your identity being stolen and impersonated by malicious actors.
Thumb rules to follow therefore include these.
- Do not post sensitive information such as names and pictures of those in your family (particularly children and your spouse) on social media. The most obvious reason being that people often use their names and identities in passwords. While this is terrible practice, why on earth would you want strangers to gawk at your family and get to know their details?
- Retain a copy of your data with you at all times. It is one thing to store everything on the cloud. But if you lose access to it and somebody gains illegal access, you will need a copy to prove ownership to law enforcement agencies.
Revisit the permissions apps have: When downloading apps, inevitably, you are asked for “Permissions” to access the microphone, camera, location, contacts, email and text messages on your smartphone. Our observations have it that most people click “Allow” without thinking twice about what they are consenting to and why.
Why do app developers need these permissions? In one line: To create a richer user profile so you can be targeted with better advertising. This is an old tactic and has been well documented. Gaming companies have a notorious reputation of doing this well. That this is unethical is one thing. In the hands of rogue actors, allowing anyone access to such personal information is deeply disconcerting.
That is why we strongly recommend revisiting the permissions to apps and the context in which they have been given.
By way of examples, a voice recording app needs access to the microphone to function. It need not be given permission to access any other data on your device. If you have Google Maps, it must access your location for it to function. Simply put, permissions matter in a certain context. Decline blanket permissions.
If you’ve already given blanket permissions and you are on an Android device, open Settings, then tap Apps & Notifications and browse through all the apps on your device. On Apple devices, tap on Settings followed by Privacy.
Re-examine those Bluetooth devices: Chances are, you have some Bluetooth device such as a headphone, smartwatch or speaker that connects to your smartphone or laptop. If these devices can connect with each other without any verification from you, anybody else can as well. The least you need to protect your data is Level 2 security. What it means is, before connecting, a PIN number is generated and that must be used by the owner to authenticate the device.
Don’t just go by the default setting: Businesses want to collect as much data from you as possible, but often they don’t want to piss off the privacy conscious. Take Cred, for example. It gives some good deals for paying credit card bills through its app. People like it for the design and flow. It’s all so smooth. But, then remember it asks for your permission to read your mail, so it can pick up the credit card statement, extract the amount you need to pay to make your experience smooth. But, don’t give up your privacy for convenience. Don’t give the app that permission. Instead, note down your credit card dues, set reminders, and enter the amount yourself. It’s not about Cred. It’s a general rule: Look for ways to access what you want, while giving as little as possible.
Sometimes, you don’t even need to trade off your privacy for convenience. Both go hand in hand. Example: Adblocker. Set aside your guilt of kicking at the guts of ad-driven business models. Install an adblocker on your browser. The ads that you see otherwise are not only a result of data collected from you, they also enable more data collection when you click on the ads. Bonus: ad blockers also stop the nagging ads in the middle of videos.
Facebook follows you even when you are not on Facebook. Many privacy conscious individuals prefer Firefox to Chrome because of extensions like Facebook Container. As Mozilla explains: “Facebook can track almost all your web activity and tie it to your Facebook identity. If that’s too much for you, the Facebook Container extension isolates your identity into a separate container tab, making it harder for Facebook to track you on the web outside of Facebook.”
How English used to be
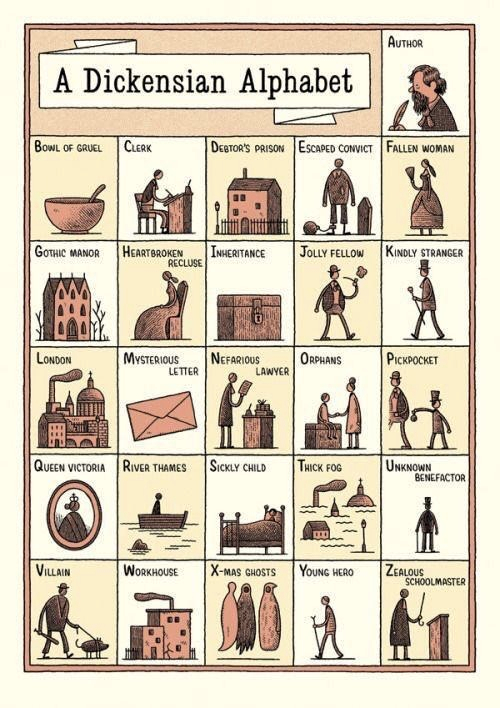
(Via Meeta Sengupta on Twitter)
Tell us what you think and find noteworthy. Head over to our our Slack channel.
And if you missed previous editions of this newsletter, they’re all archived here.
Bookmark Founding Fuel’s special section on Thriving in Volatile Times. All our stories on how individuals and businesses are responding to the pandemic until now are posted there.
Warm regards,
Team Founding Fuel



